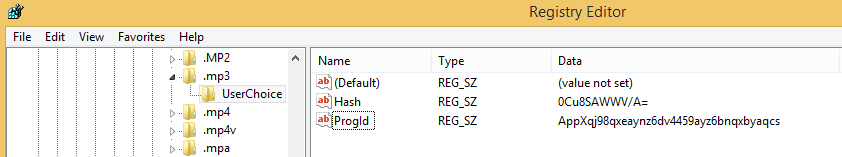
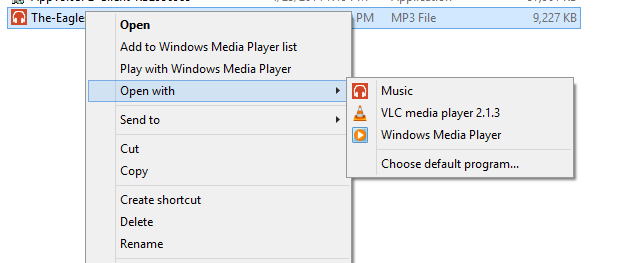
Since Windows 8 there are a lot of standard file type association set per User. For Example the file type of .mp3 is assigned to the Music Player App:
If you sequence an application which set the file type association for mp3 as standard to the new application, then the App-V client will not override this standard value mentioned above:
To avoid this, you have to create two single scripts, which have to be implemented in the DeploymentConfiguration.xml but this will only work for Domain Users and not for a local Windows User Account in App-V 5.0 sp2. This Issue has been fixed with App-V 5.0 SP2 HF4. You have to create a script not a single registry file, which should remove the association for the current user because regedit.exe is an elevated process. An elevated process can not be started by a user in an App-V configuration.xml
- Create a script which removes classes “OpenWithProgids” registry key called machine.vbs:
Dim oShell: Set oShell = CreateObject(“Wscript.Shell”)
Dim aExt, Ext
aExt = Split(“|.mp3|”, “|”) ‘for more Values use this: (“|.mp3|.mp4|.wma|”, “|”)
For Each Ext In aExt
If Ext <> “” Then
Call oShell.RegDelete(“HKEY_LOCAL_MACHINE\SOFTWARE\Classes\” & Ext & “\OpenWithProgids\”)
End If
Next - Create a script, which will remove the the Current User association and adds the required association for your file type (this will only work for VLC):
Dim oShell: Set oShell = CreateObject(“Wscript.Shell”)
Dim aExt, Ext
aExt = Split(“|.mp3|”, “|”) ‘for more Values use this: (“|.mp3|.mp4|.wma|”, “|”)
For Each Ext In aExt
If Ext <> “” Then
Call oShell.RegDelete(“HKEY_CURRENT_USER\SOFTWARE\Classes\” & Ext & “\OpenWithProgids\”)
Call oShell.RegDelete(“HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\” & Ext & “\OpenWithProgids\”)
Call oShell.RegWrite(“HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\” & Ext & “\OpenWithProgids\VLC.” & Ext & “”, 0, “REG_BINARY”)
Call oShell.RegDelete(“HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\” & Ext & “\UserChoice\”)
End If
Next - Import both files into App-V Package
- Edit DeploymenConfig.xml:
<UserScripts>
<StartVirtualEnvironment RunInVirtualEnvironment=”false”>
<Path>wscript //B “[{AppVPackageRoot}]\..\Scripts\user.vbs”</Path>
<Wait RollbackOnError=”true”/>
</StartVirtualEnvironment>
</UserScripts>
<MachineScripts>
<AddPackage>
<Path>wscript //B “[{AppVPackageRoot}]\..\Scripts\machine.vbs”</Path>
<Wait RollbackOnError=”true” Timeout=”30″/>
</AddPackage>
</MachineScripts>
Take care, that application has to be started once by each user, after that the file types are associated to your application.
For more information about package scripts, follow this guide: SHIMSs and App-V 5.0
For more information about file type associations in Windows 8, follow this guide: Windows 8: Associate a file Type or protocol with a specific app using GPO